Splunk Enterprise Security Alternative: Replace Splunk SIEM with ClickHouse + Claude Code in 2026 (Save $500K+/year)
Independent guide to replacing Splunk Enterprise Security with ClickHouse, Vector, and Claude Code-built detection-as-code. Cost breakdown, feature parity, when Splunk still wins.
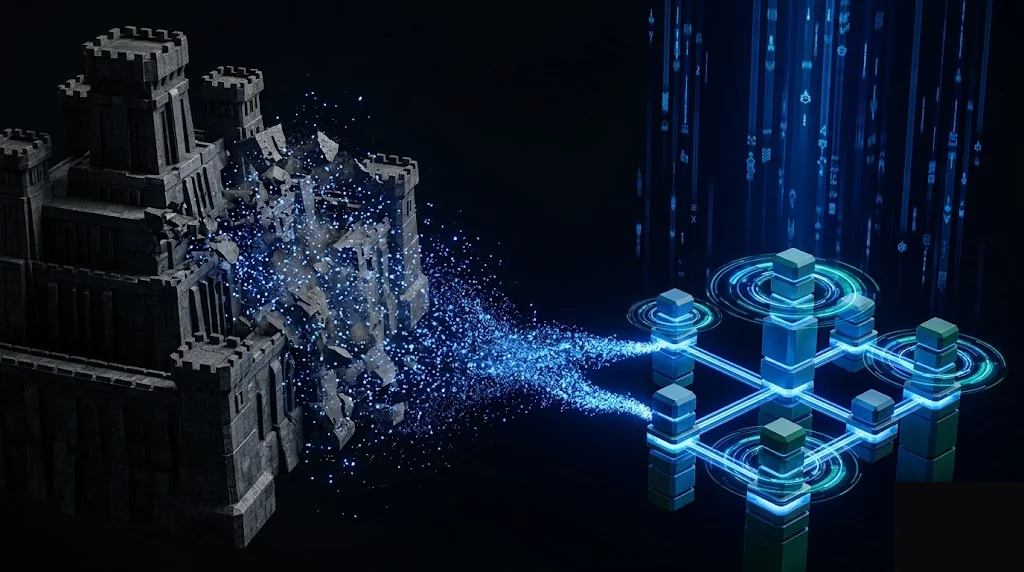
Splunk Enterprise Security is the dominant commercial SIEM. It earned that position by being early, by building Splunk Search Processing Language (SPL) into a powerful query engine, and by curating a deep library of detection content. In April 2026, with ClickHouse matching Splunk’s query performance at a fraction of the storage cost, Vector simplifying log shipping, Sigma standardizing portable detections, and Claude Code accelerating detection engineering by an order of magnitude, the case for paying Splunk has narrowed for most SOCs.
This guide is a practical comparison of Splunk Enterprise Security to a Claude Code-built SIEM stack on ClickHouse. We cover the cost breakdown, the workflow, the feature parity matrix, and the specific scenarios where paying Splunk still makes sense. Be warned: the cost differential here is the largest of any tool in our build-vs-buy series.
What Splunk Enterprise Security actually does (and what it charges)
Splunk Enterprise Security is the SIEM module on top of Splunk Enterprise (the data platform). Together they ingest security-relevant logs from across your environment, store them in indexed format, run detection searches at schedule, raise alerts to a SOC analyst UI, and integrate with SOAR for response automation.
Splunk pricing is consumption-based and notoriously expensive:
- Splunk Enterprise license: $1,800-$2,000 per GB per day ingested (committed pricing)
- Splunk Enterprise Security: additional $2,000-$3,500 per GB per day on top
- Splunk Cloud: similar effective pricing with managed infrastructure
- Workload pricing model (an alternative): per-vCPU pricing that’s typically more expensive than per-GB at production scale
For a representative mid-market SOC ingesting 100GB/day:
- Splunk Enterprise license: $200K-$400K/year
- Splunk Enterprise Security: $200K-$400K/year additional
- Total: $400K-$800K/year for a 100GB/day environment
For larger SOCs ingesting 1TB+/day, Splunk bills routinely run $5M-$50M+ per year. Public examples (Cisco’s pre-acquisition Splunk bill, various government contracts disclosed via FOIA) demonstrate the magnitude.
The pitch for paying is real: Splunk’s SPL query language is genuinely good, the curated detection content is mature, and the SOC analyst UI has been refined over a decade. SOC analysts trained on Splunk are productive immediately.
The question is whether the value is proportional to the cost. With AI-assisted development collapsing the cost of building the equivalent stack, and ClickHouse delivering Splunk-class query performance at 1/100th the storage cost, the answer for most non-regulated SOCs is now build with OSS + Claude Code.
The 75% ClickHouse + Claude Code can replicate this weekend
The OSS SIEM stack has matured into a credible Splunk replacement. The reference architecture in 2026 is:
- Collection: Vector or Fluent Bit for log shipping, with structured-data extraction
- Storage: ClickHouse for compressed columnar log storage with sub-second query latency
- Detection: Sigma rules (portable detection format) compiled to ClickHouse SQL
- Alerting: Grafana alerts or custom Python with PagerDuty/Slack integration
- Analyst UI: Grafana for dashboards, custom Python for case management or self-host an OSS case manager (TheHive, MISP)
- SOAR: n8n or self-built Python automation triggered by alerts
The actual workflow with Claude Code looks like this:
You: "Generate a Vector configuration that ships logs from all
of our AWS CloudTrail S3 buckets, our Kubernetes cluster pod
logs (via filebeat sidecar), our Linux endpoint auditd events,
and our application logs (JSON-formatted) to a ClickHouse
cluster at clickhouse.security.svc:9000. Apply schema
extraction so each log type is normalized to a common security
event schema (event_time, source_ip, user, action, resource,
result). Compress with zstd."
Claude Code generates the Vector configuration, the schema mappings, and the ClickHouse table definitions. You apply. Logs flow.
You: "Translate this Sigma rule (paste detection rule) into a
ClickHouse SQL query that runs every 5 minutes against the
last 1 hour of logs in the security_events table. Return any
matching events with their full context. Use the
materialized views I defined for source_ip aggregation to
keep the query under 500ms."
Claude Code translates Sigma rules to ClickHouse SQL. Sigma is the standard portable format, so you can pull rules from the Sigma community repository (thousands of community-maintained detections covering MITRE ATT&CK comprehensively) and translate them in seconds.
You: "Write a Claude Code skill that, given a security alert
from our detection pipeline, automatically: (1) pulls related
events from the surrounding 30-minute window, (2) enriches
the source IP with WHOIS, GeoIP, and historical reputation
data, (3) cross-references the user with HR system status
(active/leaver), (4) summarizes the situation in a Slack
incident thread, (5) suggests the most likely classification
(true positive / false positive / requires investigation) with
reasoning."
This is the SIEM workflow advantage of Claude Code at full scale. Splunk’s correlation searches and SOAR playbooks took years to build and require dedicated maintenance. Claude Code as a SOC analyst copilot does the same enrichment and triage work in hours of setup, with reasoning that traditional automation cannot match.
For threat hunting (the SOC’s exploratory analysis function), Claude Code is a step-change improvement. Analysts ask natural-language questions (“show me any service account that authenticated from a new geography in the last 24 hours”) and Claude Code writes the ClickHouse query, runs it, and explains the results.
Cost comparison: 12 months for a 100GB/day SOC ingestion environment
| Line item | Splunk Enterprise + ES | ClickHouse + Vector + Claude Code |
|---|---|---|
| Software license | $400,000-$800,000 | $0 (ClickHouse, Vector, Sigma all OSS) |
| Infrastructure (storage, compute) | included | Self-hosted ClickHouse cluster $30K-$80K/year for 100GB/day with 1-year retention |
| Engineering time to set up | 12-24 weeks of consultant-led migration | 8-16 weeks of senior SOC engineer time = $40K-$80K |
| Engineering time to maintain | ~120 hours/year (license management, content tuning, vendor liaison) | ~400-600 hours/year for stack ops, schema evolution, detection content tuning |
| Procurement and security review | 12-24 weeks | Internal change review only |
| Total Year 1 | $450K-$900K+ | $80K-$200K |
| Year 2 onward | $400K-$800K/year (often increasing) | $50K-$120K/year |
For a representative mid-market SOC, the ClickHouse + Claude Code path saves $300K-$700K in Year 1 and $280K-$680K every year after. At larger SOC scales, the savings reach into the millions.
The cost differential is so dramatic that even substantial engineering investment (a dedicated SOC platform team) is easily justified by the savings. A 5-engineer dedicated team costs roughly $1.5M-$2.5M/year fully loaded; if they save your organization $5M+/year in Splunk fees while shipping a SIEM that your analysts prefer, the ROI is overwhelming.
The 25% commercial still wins (be honest)
Splunk Enterprise Security brings real value the OSS path does not.
Curated correlation searches and detection content. Splunk Security Research maintains a deep library of pre-built detection content that maps to MITRE ATT&CK techniques. Self-built stacks pull Sigma rules from the OSS community (which is excellent and growing fast) but lack the curated context that Splunk wraps around each detection (false-positive rates, tuning guidance, response playbooks). For new SOCs without dedicated detection engineering capacity, the curated content is real value.
Polished SOC analyst UI and case management. Splunk ES ships an Investigation Workbench, case management, and SOAR integration that have been refined for years. Self-built UIs (Grafana for dashboards, TheHive or self-built case management) work but require integration effort. SOC analysts trained on Splunk experience friction switching to alternative UIs.
Vendor support and SLAs. When Splunk goes down at 3 AM during an active incident, you have a vendor with a 24/7 support contract. When self-hosted ClickHouse misbehaves, you debug it. For SOCs whose on-call burden is the binding constraint, vendor support has measurable value.
Compliance certifications. Splunk has SOC 2, FedRAMP, IL5, and various industry-specific certifications. If your SOC operates under regulatory mandates that require named-vendor SIEM tooling (certain federal contracts, certain financial regulators, healthcare in some jurisdictions), self-hosted alternatives cannot pass the regulatory gate without significant internal certification work.
Multi-tenant and acquisition handling. Splunk’s namespace and access-control models handle complex organizational structures (multiple business units, acquired subsidiaries, MSP customers) out of the box. Self-built stacks can replicate this but require careful design.
Decision framework: should you build or buy?
You should keep paying for Splunk Enterprise Security if any of these are true:
- Your SOC operates under regulatory mandates (FedRAMP, IL5, certain financial or healthcare regulators) requiring named-vendor SIEM
- Your security team relies on Splunk’s curated detection content from Splunk Security Research
- Your SOC analysts are trained on Splunk and switching costs would meaningfully degrade incident response
- Your organization is integrating acquired Splunk-using subsidiaries and consolidating to a single SIEM
- Your SOC operates 24/7 with vendor SLA dependency on Splunk support
- The Splunk license is a small fraction of the operational risk it mitigates at your scale
You should consider building with ClickHouse + Claude Code if any of these are true:
- Your annual Splunk bill exceeds $200K and is growing faster than your security headcount
- Your SOC operates outside hard regulatory SIEM mandates
- You have at least one senior platform/SOC engineer who can own the stack
- Your detection engineering is mature enough to author Sigma rules (or you can hire/contract for it)
- You want full control over data retention, query performance, and detection logic
- Your organization can tolerate a multi-month migration to capture multi-million-dollar annual savings
For most non-regulated mid-market and large enterprise SOCs, the ClickHouse + Claude Code path saves dramatic money and gives you a SIEM you fully control.
How to start (this weekend)
If you want to evaluate the build path, here is the concrete first step.
Stand up ClickHouse in a non-production environment. The Helm chart or Docker image gets you running in 30 minutes. Total time: a morning.
Ship one log source to ClickHouse via Vector. Pick a high-volume source (CloudTrail, Kubernetes audit logs, Linux syslog). Have Claude Code generate the Vector config and ClickHouse schema. Total time: an afternoon.
Run one query. Compare query performance to your current Splunk environment for the same query. ClickHouse routinely matches Splunk on query latency at 1/100th the cost.
Pull one Sigma rule from the community repo and have Claude Code translate it to ClickHouse SQL. Run it. Validate the detection works.
Estimate your full migration cost. Multiply by your detection rule count, dashboard count, and integration count. Compare to your annual Splunk bill. Decide based on real data.
If the math works, build a 6-12 month migration plan. We have helped SOCs execute Splunk-to-OSS migrations. If you want hands-on help, get in touch.
Related reading
- Detection Engineering with Sigma Rules and Claude Code
- Self-Hosted SIEM with ClickHouse: A Reference Architecture
- Hire SOC Engineers in the UAE
Disclaimer
This article is published for educational and experimental purposes. It is one engineering team’s opinion on a build-vs-buy question and is intended to help SOC, platform, and detection engineers think through the trade-offs of AI-assisted SIEM operations. It is not a procurement recommendation, a buyer’s guide, or a substitute for independent evaluation.
Pricing figures cited in this post for Splunk are approximations based on Splunk’s published pricing documentation, customer-reported procurement disclosures, public-sector contract records, and conversations with SOC leaders. They are not confirmed by Splunk and may not reflect current contract terms, regional pricing, volume discounts, or negotiated rates. The very-large-bill examples (referenced in the introduction) are based on publicly-reported customer experiences and should not be interpreted as representative outcomes. Readers should obtain current pricing directly from Splunk before making any procurement or budget decision.
Feature comparisons reflect the author’s understanding of each tool’s capabilities at the time of writing. Both commercial products and open-source projects evolve continuously; specific features, limitations, integrations, and certifications may have changed since publication. The “75%/25%” framing throughout this post is intentionally illustrative, not a precise quantitative claim of feature parity.
Code examples and Claude Code workflows shown in this post are illustrative starting points, not turnkey production software. Implementing any SIEM stack in production requires engineering judgment, security review, operational hardening, on-call expertise, and ongoing maintenance that this post does not attempt to provide. Self-hosted SIEM has real operational costs that must be weighed against vendor SaaS costs, especially around availability, scale, and detection engineering capacity.
Splunk, Splunk Enterprise Security, ClickHouse, Vector, Sigma, TheHive, MISP, Grafana, n8n, and all other product and company names mentioned in this post are trademarks or registered trademarks of their respective owners. The author and publisher are not affiliated with, endorsed by, sponsored by, or in any commercial relationship with Splunk, Cisco, ClickHouse Inc., Datadog, Grafana Labs, the Sigma project, or any other vendor mentioned. Mentions are nominative and used for descriptive purposes only.
This post does not constitute legal, financial, or investment advice. Readers acting on any guidance in this post do so at their own risk and should consult qualified professionals for decisions material to their organization.
Corrections, factual updates, and good-faith disputes from any party named in this post are welcome — please contact us and we will review and update the post promptly where warranted.
Frequently Asked Questions
Is there a free alternative to Splunk Enterprise Security?
Yes, for the data and detection layer. ClickHouse (OSS, OLAP database) for log storage, Vector (Datadog, OSS) for log shipping, Sigma (OSS) for portable detection rules, and Claude Code as a detection engineering copilot replicate roughly 70-80% of Splunk Enterprise Security functionality at zero per-GB-ingested cost. Add Grafana for dashboards and you have a complete SIEM stack. The 20-30% you give up is Splunk's curated correlation searches, vendor support, and the polished SOC analyst UI. For most teams, the cost differential is too large to ignore.
How much does Splunk Enterprise Security cost compared to a Claude Code build?
Splunk pricing is consumption-based and notoriously expensive. Headline rates: Splunk Enterprise license is $1,800-$2,000 per GB per day ingested (committed pricing); Splunk Enterprise Security adds another $2,000-$3,500 per GB per day on top. A 100GB/day SOC ingestion environment runs $400,000-$700,000 per year for Enterprise plus another $700K-$1.2M for ES on top. Splunk Cloud pricing is similar. Public Splunk bills hitting $5M-$50M/year are common at large enterprises. The Claude Code SIEM stack on equivalent infrastructure runs $30K-$100K/year for storage and compute, plus ~$240/year per analyst for Claude Pro. Year-1 total fully loaded is typically $80K-$200K.
What does Splunk Enterprise Security do that Claude Code cannot replicate?
Splunk ES brings four things a self-built stack does not: (1) curated correlation searches and detection content from Splunk Security Research that map to MITRE ATT&CK, (2) vendor-managed analyst UI with case management, investigation workflows, and SOAR integration, (3) SLAs and 24/7 vendor support for SOC operations, (4) compliance certifications (SOC 2, FedRAMP, IL5) that simplify regulated-industry deployment. If your SOC operates under regulatory mandates that require named vendor tooling, Splunk is uniquely positioned. For most other teams, the OSS stack competes on capability and crushes on cost.
How long does it take to replace Splunk with ClickHouse + Claude Code?
A senior SOC engineer working with Claude Code can stand up a working SIEM stack in 4-8 weeks. The stack: Vector ships logs from sources to ClickHouse, ClickHouse stores compressed logs queryable in milliseconds, Sigma rules express portable detections, Claude Code writes Sigma-to-ClickHouse query translations and triages alerts. Add another 4-8 weeks for SOAR-equivalent automation, case management, and analyst dashboards. Total roughly 2-4 months vs. 6-12 months of typical Splunk migration plus annual license renewal cycles.
Is the ClickHouse + Claude Code SIEM production-ready?
ClickHouse is production-grade and used at scale by major SOCs (including Cloudflare's threat intelligence platform, Uber's data infrastructure, and many others). Vector is a Datadog-maintained OSS log shipper used in production at significant scale. Sigma is the de facto standard portable detection rule format. The work that determines success is the detection engineering and analyst workflow layer, where Claude Code dramatically accelerates rule writing, alert triage, and threat hunting queries. Most SOCs reach production-ready quality in 8-16 weeks of part-time work.
When should we still pay for Splunk Enterprise Security instead of building?
Pay for Splunk when: (1) your SOC operates under regulatory mandates (FedRAMP, IL5, certain financial regulators) that require named vendor SIEM tooling, (2) your security team relies on Splunk's curated detection content from Splunk Security Research, (3) your SOC analysts will not adopt a SIEM that lacks the polished analyst UI and case management workflows they are trained on, (4) your organization is acquiring Splunk-using subsidiaries that need a single SIEM, or (5) the Splunk license is a small fraction of the breach risk it mitigates at your operational scale. For everyone else — and that is most non-regulated SOCs — ClickHouse + Claude Code-built detection saves dramatic money and gives you a SIEM you fully control.
Complementary NomadX Services
Defend AI with AI
Start with a free AI SOC Readiness Assessment and see where your AI defenses stand.
Assess Your AI SOC Readiness